Setup of iDIN
Integration with iDIN is done similarly to other Signicat's eIDs supported by the eID and Wallet Hub. This page describes the process of setting up iDIN.
For general information about integrating with Signicat, see the eID and Wallet Hub Quick start guide.
Initial preparations
If you do not have an account already, then you need to sign up to the Signicat Dashboard for free and complete the initial preparations. To do this:
- Sign up to the Signicat Dashboard and register your profile.
- Ensure that you have created an organisation.
- Create an account. To do this:
- Go to Signicat Dashboard > Organisation, then select + Add account.
- Enter an account name, choose the type of account that you want to create, then select Create.
- Create a domain. To do this:
- Go to Signicat Dashboard > Settings > Domains, then select + Add domain.
- To create a standard domain, enter a domain name. Then, select Add domain.
- To create a custom domain, follow the instructions in the Custom domains documentation.
We recommend that you create a sandbox account to test our services before going live. Sandbox and production accounts must be set up separately.
Sign agreements
To get started with iDIN in a sandbox account where you can already test authentications, you may skip this step.
Before you can start integrating iDIN in production, you must sign an agreement with Signicat and obtain access to the production environment. To do this, contact our digital identity experts.
Once you receive access to iDIN in production, ensure you:
- Create a production account.
- Add a domain.
- Add iDIN in the Signicat Dashboard and set up a connection, as explained in the rest of this guide.
Add iDIN
To add iDIN to your account in the Signicat Dashboard, follow these steps:
- Go to Products > eID and Wallet Hub > eIDs.
- Select + Add new.
- Choose iDIN from the list.
- Now, you need to configure iDIN, as explained in the Configuring Signicat DISP section below.
Configuring Signicat DISP
In the Dashboard, you can configure the following Digital Identity Service Provider (DISP) settings:
- Standard > Include only when scoped checkbox: If ticked, iDIN will not be visible by default on the eID selection screen, unless you specify it explicitly with IdP scoping.
- Advanced > Select attribute filter: Select an attribute filter to control which attributes to include, or exclude, from the response. To create attribute filters in the Dashboard, navigate to Products > eID and Wallet Hub > Advanced > Attribute filters.
- Advanced > Receive housenumber suffix as a separate attribute: If ticked, you will receive the house number suffix as an additional field in the Address object.
- Advanced > Response attribute mappings: Allows you to rename the attributes you receive in the response body from an authentication. For example, you can rename
idin-lastNametosurname. You can provide none or multiple name-to-name mappings. This option works best with SAML.OIDCYou must not rename OIDC attributes, since they are standardised and normalised attributes.
To activate iDIN in your account with these settings, select Add. Verify that iDIN is shown with status "Active" in the list of eIDs available for your account.
We provide support for iDIN QR code flows. Learn more in the iDIN QR code flow documentation.
Try it out
To run a test authentication with iDIN, visit the Test information guide.
We recommend you also test your integration with iDIN after you create a connection with an authentication protocol. You can find instructions for setting up an authentication protocol in the next section below.
Set up a connection with a protocol
To establish a connection between Signicat and your application, you need to use an authentication protocol. Note that you only need to connect to Signicat (eID and Wallet Hub) servers. Signicat handles the connection with iDIN separately, therefore acting as a message broker between your application and iDIN.
Supported authentication protocols
Signicat supports the standard OpenID Connect (OIDC) and SAML 2.0 protocols. In addition, we offer our bespoke Signicat Authentication REST API.
The protocol you choose depends on your goals and preferences. The Authentication REST API provides flexibility and an easy setup. Otherwise, we recommend OIDC, since SAML 2.0 is much more complex to implement and usually requires a federation agent. OIDC is an industry standard with managed user sessions, unlike the Authentication REST API.
For more information about the different protocol types, see the Signicat eID and Wallet Hub documentation. To learn more about these authentication protocols, see the Signicat eID and Wallet Hub documentation.
Set up the protocol
For information on how to set up an integration with a protocol, see the protocol-specific guides:
For more information about the different protocol types, see the Signicat eID and Wallet Hub documentation.
Data and attributes
To learn more about attributes, scopes and claims supported by each authentication protocol, visit the Attributes reference page.
To obtain the list of iDIN issuer banks active in your account, go to https://<YOUR_SIGNICAT_DOMAIN>/broker/authn/idin/issuers. Note that <YOUR_SIGNICAT_DOMAIN> is the domain defined in the Signicat Dashboard > Domains page.
Issuer bank selection screen
The iDIN Merchant Implemention Guide (EN) describes what regulations you, as a service provider, must follow when implementing iDIN in your applications. Importantly, note the following:
- The iDIN issuer bank selection screen must include a dropdown list that shows the names of the issuer banks part of the iDIN network. The first element in the list must state "Kies uw bank…" (or "Choose your bank…" in English) and be pre-selected, by default.
- All iDIN issuer banks must receive fair representation in the dropdown list.
- You are not allowed to grey out or remove issuer banks temporarily from the dropdown selection list.
When integrating with iDIN through Signicat, you can choose between two options:
- Rely on the built-in Signicat issuer bank selection screen. This redirects the end-users automatically to their bank authentication portal.
- Handle the issuer bank selection list in your own custom graphical user interface and then send a request to redirect the end-users to their specific bank authentication portal.
These scenarios are discussed below.
Built-in Signicat selection screen
By default, an authentication request with iDIN routes your end-users to the Signicat built-in issuer bank selection screen. Below, you find an example.
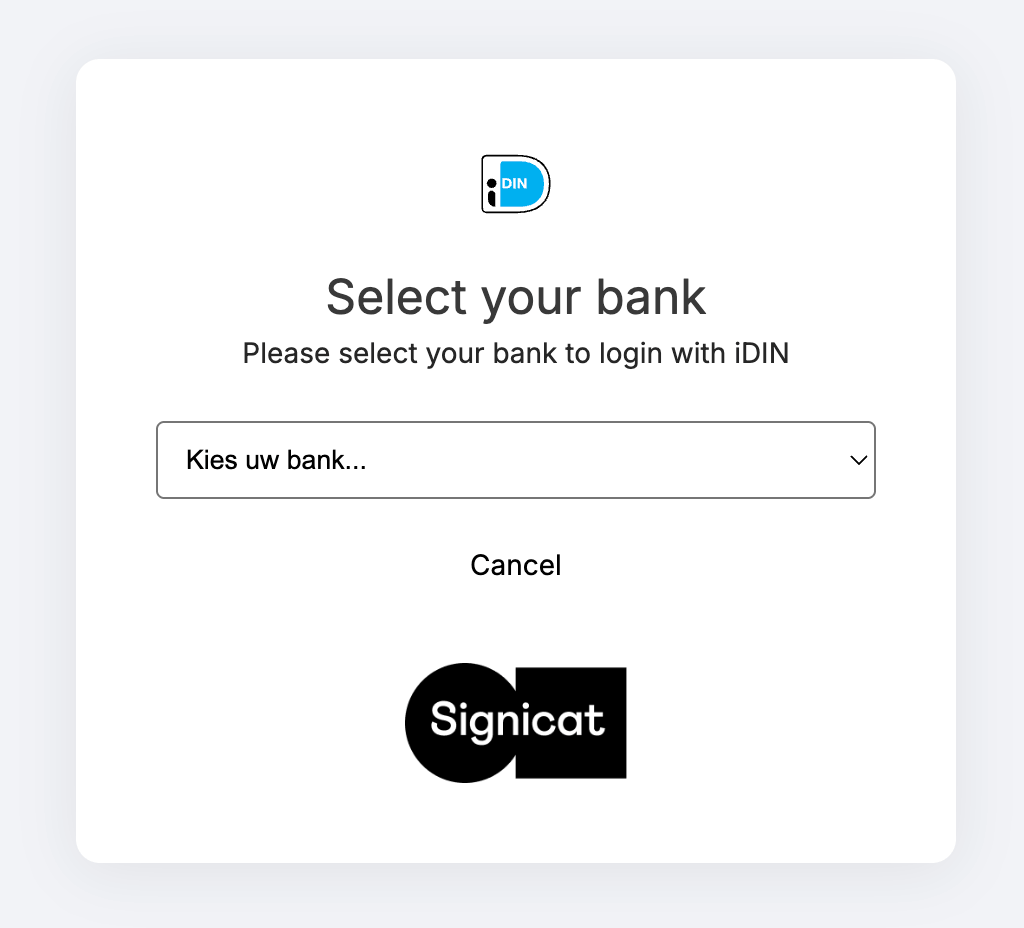
Signicat's built-in issuer bank selection screen for iDIN.
Your typical authentication request would look like this:
- OpenID Connect
- SAML 2.0
- Authentication REST API
https://<YOUR_SIGNICAT_DOMAIN>/auth/open/connect/authorize?
&client_id=<OIDC_CLIENT_ID>
&response_type=code
&redirect_uri=<REDIRECT_URI>
&state=1599045135410-jFe
&scope=openid%20profile
&acr_values=idp:idin
&prompt=login
&nonce=1599046102647-dv4
Note how the ACR values (acr_values=idp:idin) automatically redirect your end-users to iDIN by skipping the eID selection screen. This is known as IdP scoping.
Routing to issuer bank portal
If you handle the issuer bank selection list in a custom graphical user interface on your side, you can build your authentication request to automatically direct the end-user to the bank authentication portal. Note that in this case the built-in Signicat issuer bank selection screen is skipped and not displayed to your end-users.
To route your end-users directly to their bank authentication portal, you can use provider scoping, as shown below:
- OpenID Connect
- SAML 2.0
- Authentication REST API
To route your end-users directly to their bank authentication portal, pass the idin_idp parameter in the ACR values. For example, to direct to ING bank, pass the following query parameter in your authorisation request:
acr_values=idp:idin idin_idp:INGBNL2A
To obtain the list of iDIN issuer banks active in your account, go to https://<YOUR_SIGNICAT_DOMAIN>/broker/authn/idin/issuers. Note that <YOUR_SIGNICAT_DOMAIN> is the domain defined in the Signicat Dashboard > Domains page.