How to renew PKIo certificates
PKIo certificates have a set expiry date and must be renewed periodically for security purposes. Renewing an expiring certificate requires to update your configuration in the Signicat Dashboard and communicate the change with Logius.
This page outlines the steps to follow when you need to renew an expiring PKIo certificate.
1. Create a CSR in the Dashboard
A Certificate Signing Request (CSR) contains identifying information about your organisation. When applying for a PKIo certificate, you need to create a CSR and share it with a Certificate Authority (CA). Doing this allows the CA to verify your business and issue a PKIo certificate.
To create a CSR in the Signicat Dashboard, follow these steps:
- Go to the Signicat Dashboard > Organisation management.
- Select the account to create a CSR for.
- In the account management page, select Signing Certificates.
- In Certificate Signing Requests, select Create.
- Fill in the fields in the form:
- Select Create to generate the Certificate Signing Request (CSR) based on the information you submitted.
- Select Download to download the newly created CSR.
A CSR is represented as a Base64 encoded string:
-----BEGIN CERTIFICATE REQUEST-----
...Base64-encoded string...
-----END CERTIFICATE REQUEST-----
Remember that you need to share the CSR with the Certificate Authority (CA) when you apply for a PKIo certificate, as explained in the next step below.
2. Purchase a new PKIo certificate
PKIo certificates are Public Key Infrastructure (PKI) certificates used to cryptographically sign messages between Signicat and the network infrastructure of Logius.
Learn more about PKIo certificates at https://cert.pkioverheid.nl/ and https://www.logius.nl/english/pkioverheid.
PKIo certificates are required to connect to DigiD, DigiD CombiConnect or eHerkenning. To integrate successfully, you need to purchase and configure two separate certificates:
- One PKIo certificate for sandbox (preproduction)
- One PKIo certificate for production
Note that obtaining a new PKIo certificate may take up to five working days.
Supported PKIo certificate types
The PKIo certificates must be of one of these types:
- Staat der Nederlanden - G4 Root Priv G-Other - 2024 (until 2039)
- G4 Intm Priv G-Other LP - 2024 (recommended)
- Staat der Nederlanden Private Root CA - G1 (until 2028)
- Staat der Nederlanden Private Services CA - G1
- Staat der Nederlanden Root CA - G3 (until 2028)
- Staat der Nederlanden Organization Services CA - 2023
- Staat der Nederlanden Organisatie Services CA - G3
Certificate providers
You can purchase PKIo certificates from any of the Trust Service Providers (TSPs) approved by Logius. For a list of authorised providers, see the PKIoverheidcertificaat aanvragen page.
To purchase Digidentity certificates, Signicat must first generate the appropriate Certificate Signing Request (CSR) for you. Please contact us by creating a support ticket in the Signicat Dashboard.
When purchasing PKIo certificates, make sure that:
- You only use the Certificate Signing Request (CSR) obtained in the Signicat Dashboard. If you purchase the certificates independently or without the CSR, your integration will fail.
- You purchase two separate PKIoverheid (PKIo) certificates: one for the sandbox environment and one for the production environment.
- The type of PKIo certificate is one of the Supported PKIo certificate types.
When purchasing a certificate, you should explicitly ask the provider to use the CSR you generated in the Signicat Dashboard.
You can find more instructions to guide you with purchasing PKIo certificates from a trusted provider on the Logius website at PKIoverheid-certificaat aanvragen.
The importance of certificates is increasing and regulations around certificates are changing. Learn more about the new generation of PKIo certificates.
3. Upload PKIo certificates in the Dashboard
Once you have purchased and received the PKIo certificates from a certificate provider, you need to upload the public part of the certificates (.pem or .cer file extension) to the Signicat Dashboard.
To upload a PKIo certificate to the Signicat Dashboard, do the following:
- Navigate to Account management > Signing Certificates.
- In the Signing Certificates section, select Upload certificate to upload the PKIo certificate from your device.
Alternatively, you can send us the new PKIo certificate either by creating a support ticket in the Signicat Dashboard or by contacting your onboarding manager.
Please allow up to 4 hours for the certificates to become active and ready for use. If you require expedited processing, contact us by creating a support ticket in the Signicat Dashboard and request priority handling.
When you upload a PKIo certificate, you store the (public) PKIo certificate in the Signicat Dashboard infrastructure. To view your certificates, do the following:
- Go to Signicat Dashboard > Products > eID Hub.
- In the left-side menu, navigate to Advanced > Certificates.
- Here, you can review your active certificates and access more details, such as issuer and validity window.
4. Get Signicat metadata
To switch your connection from an expiring PKIo certificate to a new PKIo certificate, you need to share the metadata of the new PKIo certificate with Logius. To do this, you need to complete these steps:
- Download a metadata containing the details of the new PKIo certificate.
- Submit a change request to Logius to update your connection configuration with the metadata of the new certificate.
The instructions below explain how to achieve this.
It is important to note that downtime is to be expected, while switching DigiD connections from one certificate to another. This is due to Logius infrastructure design which supports one certificate at a time.
Note that authentication transactions will fail while you are waiting for Logius to update your connection with your new certificate metadata. It is recommended that you inform your end-users promptly.
To avoid downtime while retrieving the metadata for your new PKIo certificate, advanced users can follow the Advanced flow to reduce downtime steps below.
To get the Signicat metadata for your PKIo certificate, do the following
- In the Signicat Dashboard, navigate to Products > eID and Wallet Hub > eIDs.
- In the left menu, navigate to Advanced > Certificates. Here you can view your active certificates. The active (in use) certificate is marked by the radio button.
- Select the new PKIo certificate you intend to switch to and set it to active.
Important
While the new PKIo certificate is set to active, transactions with your existing DigiD connection will fail until you reset the old (expiring) certificate to active, as explained in step 7 below.
To avoid downtime while retrieving the metadata for your new PKIo certificate, advanced users can follow the Advanced flow to reduce downtime below.
- In the left menu, navigate to eIDs and choose DigiD from the list.
- In the DigiD configuration, click Get Signicat metadata. This opens your metadata, which includes your new PKIo certificate, in a new tab in your browser.
- Save the metadata as an XML file. You can do this by right-clicking in the page and selecting "Save as...". Then, save the XML file on your local device.
- Important: In the left menu, go back to Advanced > Certificates and switch back to your expiring certificate. This is to avoid downtime while Logius approves your new metadata request.
Reminder
Remember to switch back to the expiring certificate as explained in step 7 above. After you switch back to the expiring certificate, your end-users can successfully complete authentication transactions.
Advanced flow to reduce downtime
You can avoid downtime while retrieving the metadata for your new PKIo certificate by following the advanced guide below.
Note that this will only mitigate downtime to obtain the new metadata. You should still expect downtime while you wait for Logius to update your connection, as explained in 5. Submit change to Logius.
Advanced flow - How to reduce downtime
- Obtain the following properties from your new PKIo certificate:
- SHA 256 fingerprint:
openssl x509 -noout -fingerprint -sha256 -inform pem -in <YOUR_PKIO_CERT.pem> | sed 's/SHA256 Fingerprint=//g' | tr -d ':' | tr '[:upper:]' '[:lower:]'
- Base64 encoded certificate string:
sed '/---/d' _.qwant.com.pem | tr -d '\n\r'; echo
Format guidelinesMake sure you remove enclosures (
-----BEGIN CERTIFICATE-----and-----END CERTIFICATE-----) and any new line character from the certificate string. - SHA 256 fingerprint:
- In the Signicat Dashboard, navigate to Products > eID and Wallet Hub > eIDs.
- In the left menu, navigate to eIDs and choose DigiD from the list.
- In the DigiD configuration, click Get Signicat metadata. This opens your existing connection metadata, including your expiring PKIo certificate details, in a new tab in your browser.
- Save the metadata as an XML file. You can do this by right-clicking in the page and selecting "Save as...". Then, save the XML file on your local device.
- Now, open the XML file with a compatible text editor.
- Edit the values of the following XML fields:
SPSSODescriptor>KeyDescriptor>KeyInfo>KeyName: Substitute the value with the SHA 256 fingerprint of you new PKIo certificate that you obtained in step 1.SPSSODescriptor>KeyDescriptor>KeyInfo>X509Data>X509Certificate: Substitute the value with the Base64 encoded certificate string of you new PKIo certificate that you obtained in step 1.
- Save the metadata file with the new PKIo certificate values. You need to submit this XML file to Logius, as explained below.
5. Submit change to Logius
To update your DigiD connection with the new PKIo certificate, you need to submit a change request with the metadata file containing your new PKIo certificate details. To do this, you need to fill in a form on the Logius website.
Note that it may take a few days for Logius to process the change. You can request the change to occur at a specific time window during office hours.
To submit the change request to Logius, do the following:
- Go to https://www.logius.nl/domeinen/toegang/digid/wijzigingsformulier-digid.
- Fill in the change form (wijzigingsformulier) with the details of your request and upload the metadata for the new PKIo certificate. For example, fill in:
- Op welk koppelvlak bent u aangesloten?: SAML
- Wat is uw wijziging?:
Ik wil de metadata vervangen (bijvoorbeeld bij certificaatwissel) - Enter the following depending on your scenario:
- Environment type (omgeving)
- Date (datum)
- Time (tijd)
- Metadata: Provide the XML file with your metadata.
- Submit the form to Logius and prepare for switching to the new certificate.
You can view an example below:
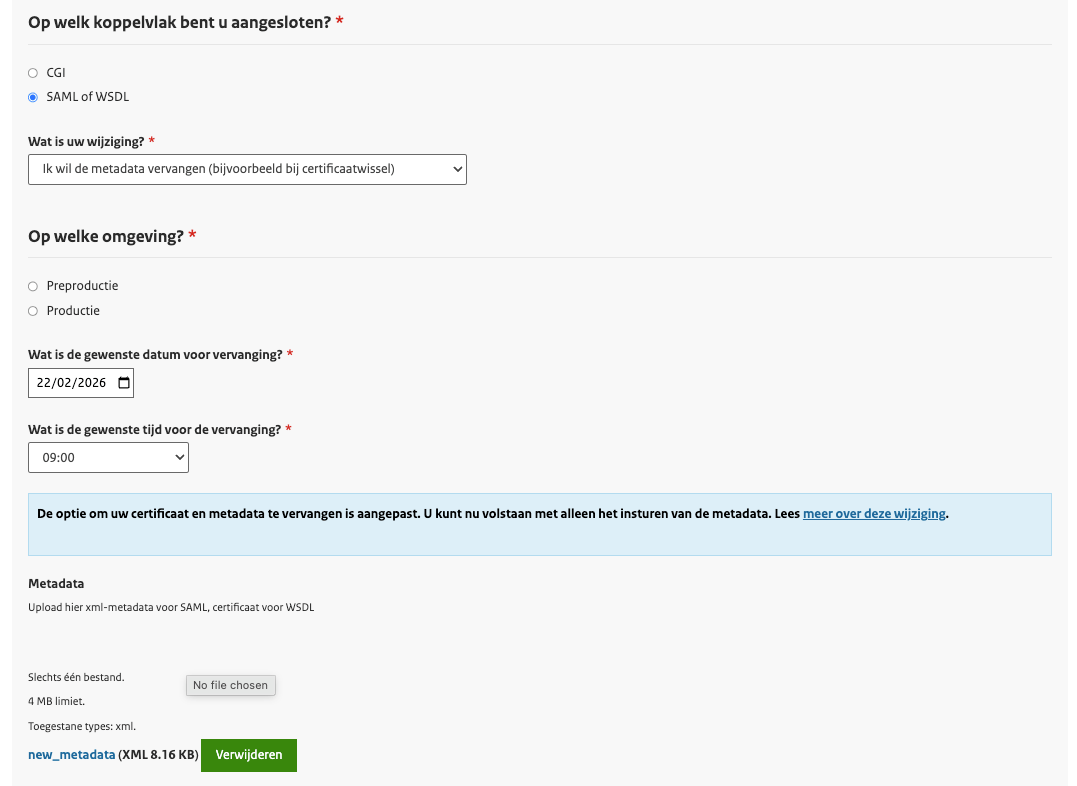
DigiD change form (wijzigingsformulier)
6. Switching to the new certificate
We recommend you communicate the incoming maintenance with your end-users on your website or application. For example, you could display a banner that warns users about potential downtime during the time window you agreed with Logius to update your connection to use the new PKIo certificate.
It is important that you time your certificate switch with Logius to reduce any potential downtime.
When you receive confirmation from Logius and are ready to switch to using the new PKIo certificate, do the following:
- In the Signicat Dashboard, navigate to Products > eID and Wallet Hub > eIDs.
- In the left menu, navigate to Advanced > Certificates.
- Select the new PKIo certificate you intend to switch to and set it to active.
Once activated, your DigiD connection will automatically begin using the new PKIo certificate. Authentication transactions will be using the newly activated PKIo certificate going forward.