Shared computer login
Use case
You are looking for a secure way for your employees to log in to a shared company computer or shared workstation.
Rather than dealing with shared passwords, forgotten passwords, or cumbersome One-Time Passwords (OTPs), employees can use a passkey stored on their own personal mobile device to quickly and securely log in to the shared workstation.
This use case relies on cross-device authentication which bridges the gap between the shared computer and the end-user's personal mobile device, while maintaining high security.
How it works
Meet Jane, one of your active employees who has set up a passkey on their personal mobile device for your company portal. Jane needs to log in to a shared computer at the office to access your internal services.
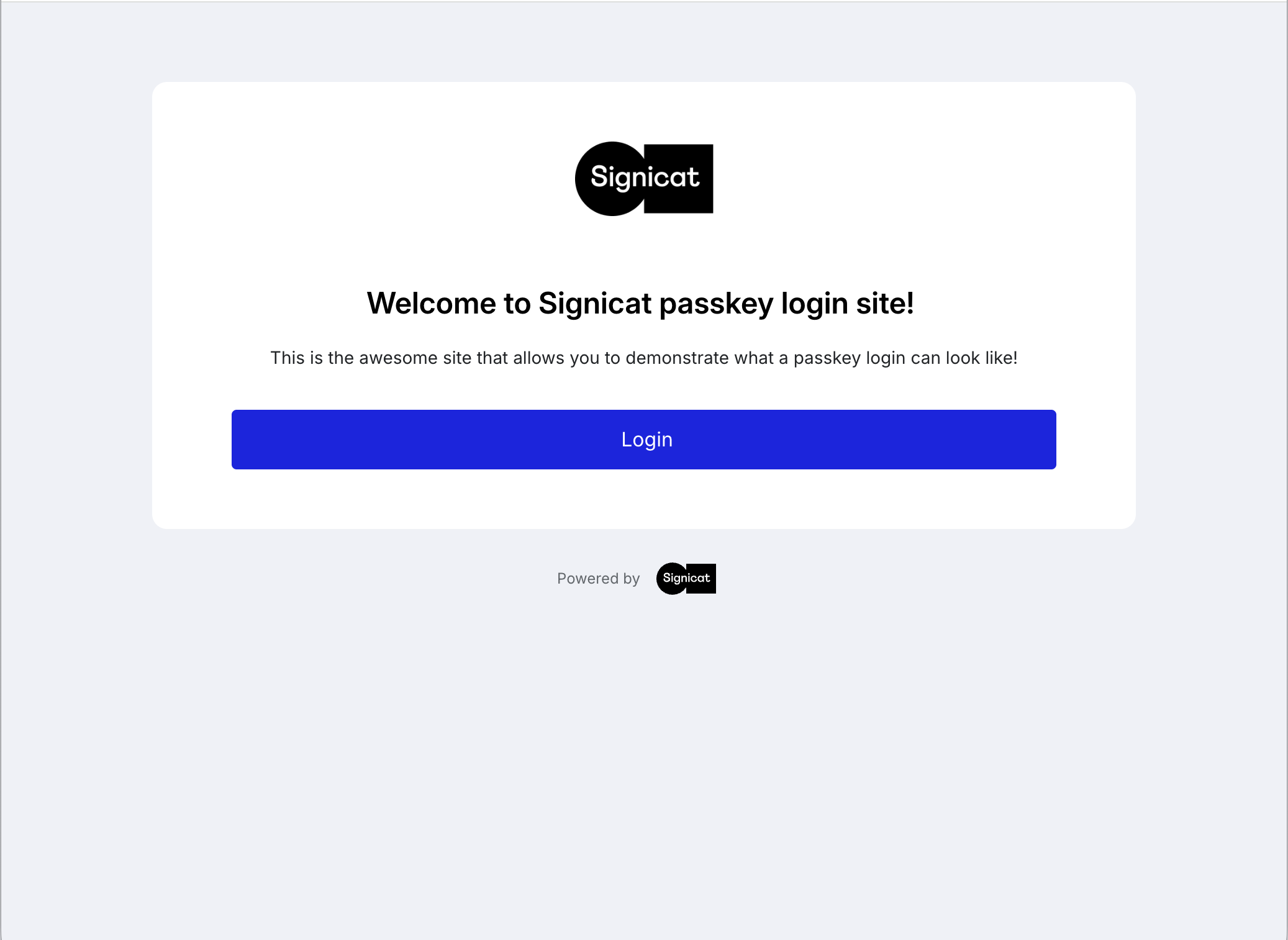
- Jane visits your internal portal on the shared computer and clicks the login button.
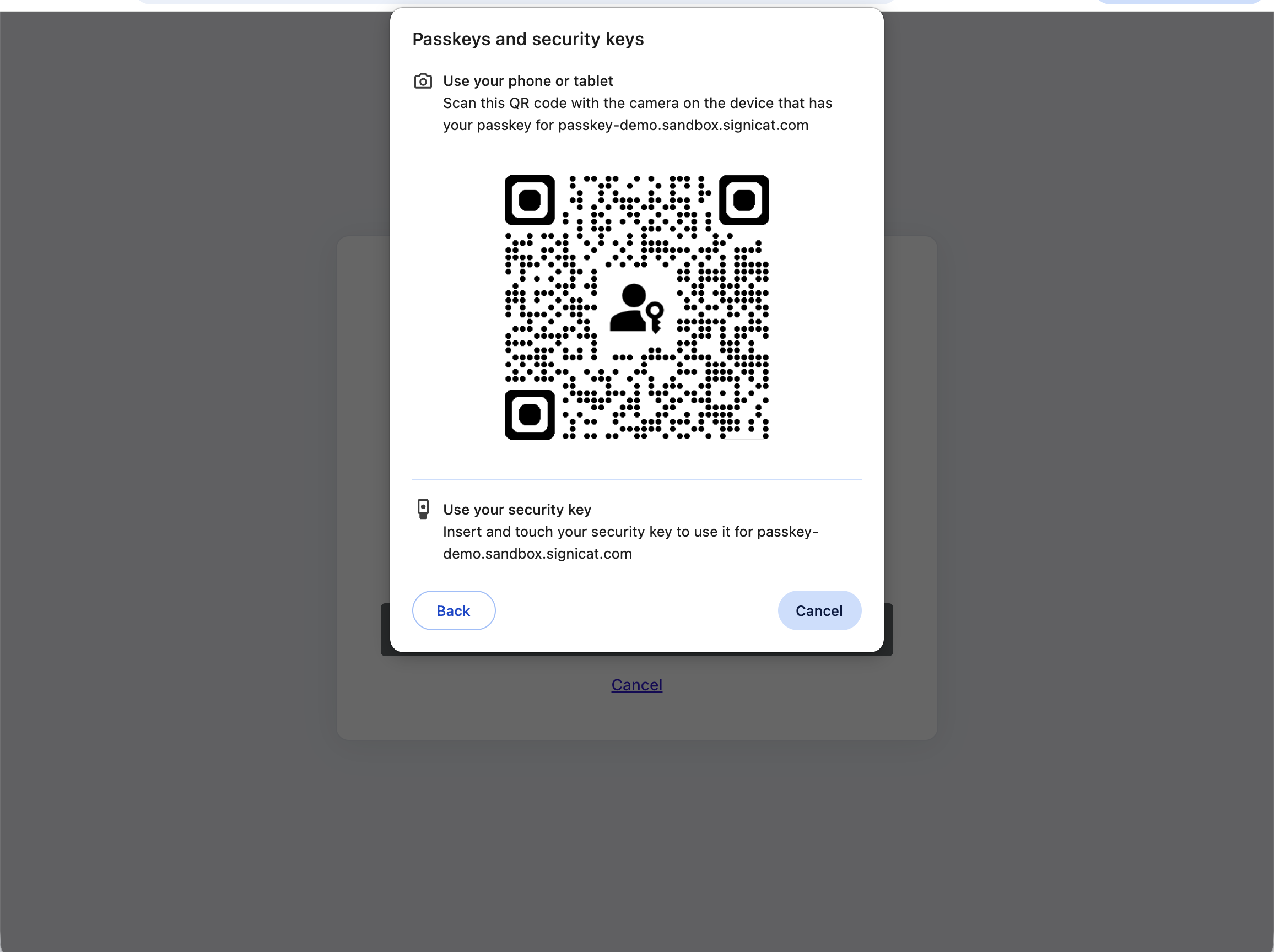
- The browser displays a QR code and prompts her to use a passkey from another device.
- Jane scans the QR code using her mobile device's camera.
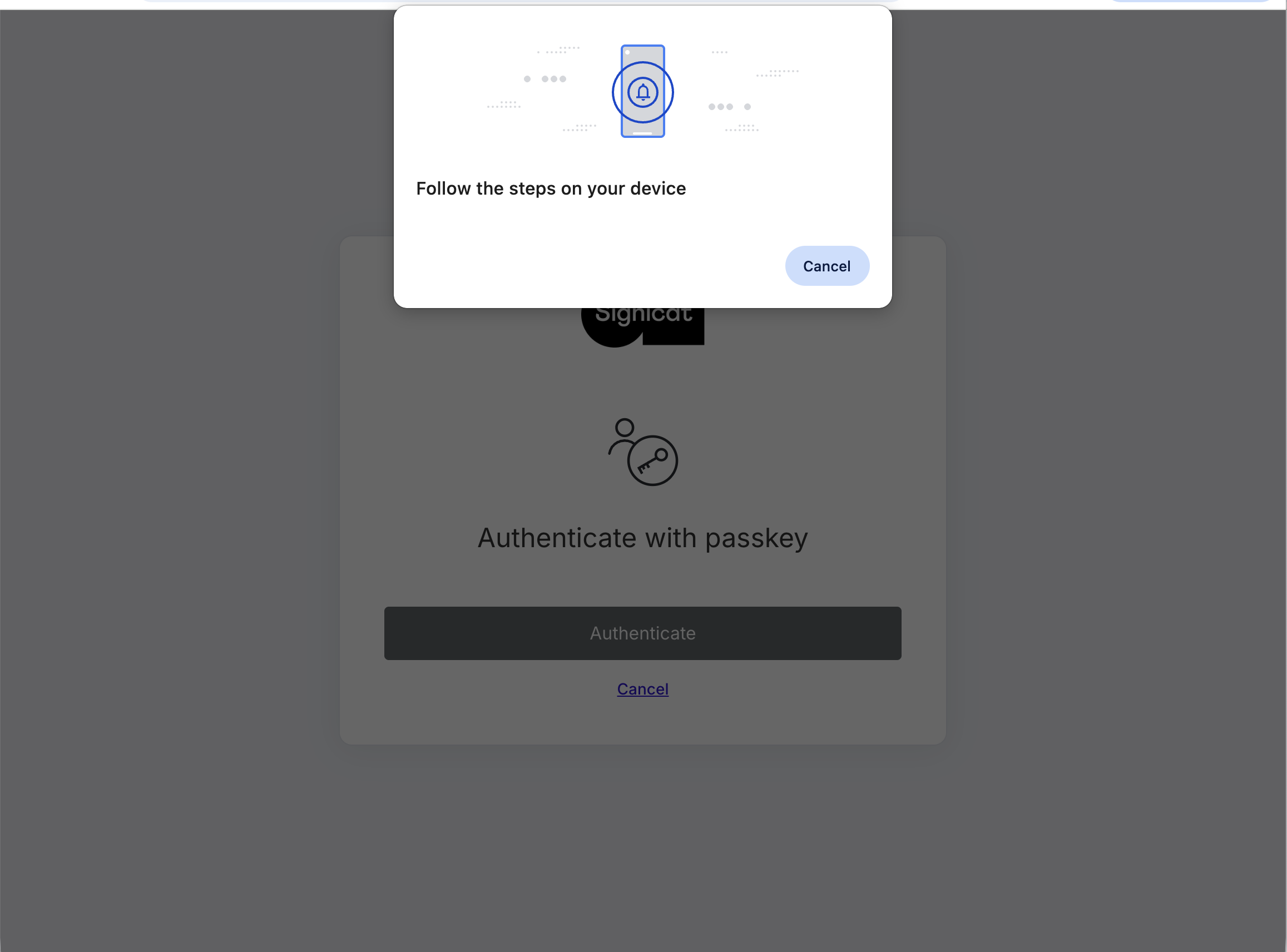
- Her mobile device connects via Bluetooth to verify proximity and prompts her to authenticate using her passkey.
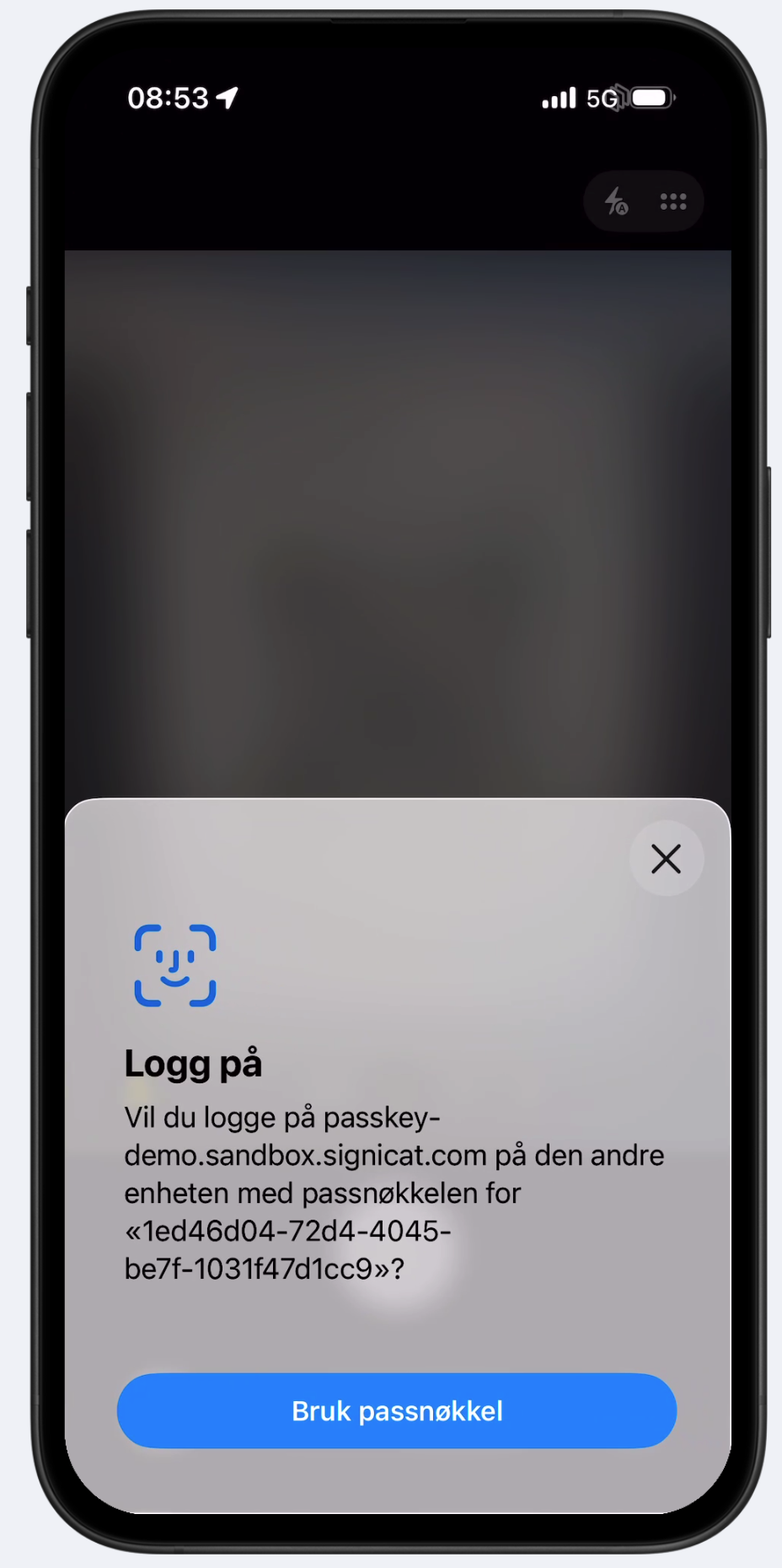
- Jane uses her mobile device's local authentication to approve the login.
What does this mean?
An example of a local authentication on the mobile device could be Face ID or Touch ID.
- The authentication is successful, and Jane is logged into the internal portal on the shared computer.
Jane has now securely authenticated herself on the shared computer using her personal mobile device, without needing a password.
What it looks like
The following diagram illustrates what the cross-device authentication flow could look like using a passkey from the perspective of an employee.
Cross-device authentication
Implementation
This flow assumes that you are using ReuseID with Passkeys authentication, and that the employee has an active ReuseID user with a registered passkey on their personal device.
The following flow is a suggestion on how to implement passkey authentication for a shared computer, leveraging the Signicat ReuseID API:
- The employee initiates the login process by clicking a button on the shared computer's browser.
- Your server starts an authentication process by calling the Signicat ReuseID API.
- Signicat generates a challenge and returns an
idpRedirectUri. - The shared computer opens the
idpRedirectUri, which prompts the browser to request a passkey authentication. - The employee authenticates by scanning a QR code with their personal mobile device.
- The personal mobile device authenticator generates an assertion and sends it to Signicat.
- Signicat verifies the assertion and redirects the browser on the shared computer to your specified redirect URL upon completion.
- Signicat sends a callback to your server containing the authentication response.
- Your server grants the employee access to their account on the shared computer based on the callback.
Sequence diagram
Sequence diagram showing passkey authentication on a shared computer