How it works
A passkey is made up of two keys:
- Private key: This is securely stored with the end-user.
- Public key: This shared and stored server side (Signicat).
The key pair is created by the end-user's key provider used in their browser. Some examples of key providers are:
- Apple
- Microsoft
- A password manager, for example 1Password
- FIDO2 hardware tokens, for example YubiKeys
Once the passkey key pair has been created by the key provider, the private key is safely stored in the end-user's key provider ecosystem.
As it is managed by the key provider ecosystem, the passkey syncs securely across all of the end-user's devices. This means that your end-users can log in from their mobile phone, tablet, or laptop with ease.
A key provider ecosystem for passkeys refers to entities responsible for creating, managing, storing and synchronising passkeys across devices.
Examples of these entities include Apple iCloud Keychain and Google Password Manager.
What makes passkeys secure?
The Signicat passkeys service is built on three powerful technologies:
- FIDO2: An open security standard supported by Google, Apple, Microsoft, and others.
- WebAuthn: A W3C standard that lets browsers use secure keys instead of passwords.
- Signicat: A European leader in digital identity services; offering reusable digital identities and combining authentication with identity proofing.
Technical flow
Passkey authentication is based on the WebAuthn standard, which is part of the FIDO2 protocol suite.
It uses public key cryptography with a challenge-response mechanism, where the end-user signs a one-time challenge (a nonce) using their private key after biometric verification.
For a high-level explanation of how a passkey authentication works, see the steps below:
- The end-user navigates to a website in their browser, then clicks Log in with passkey.
- They are redirected to the Signicat login page. Here, they click Authenticate.
- Signicat sends a challenge (a nonce) to the end-user's browser. The end-user does not see the challenge.
- The end-user authenticates with biometrics on their device, to unlock the private key that signs the challenge.
- The browser sends the signed challenge to Signicat.
- Signicat verifies the signed challenge with the public key, then redirects the end-user back to the website with the result of the login.
End-user flow
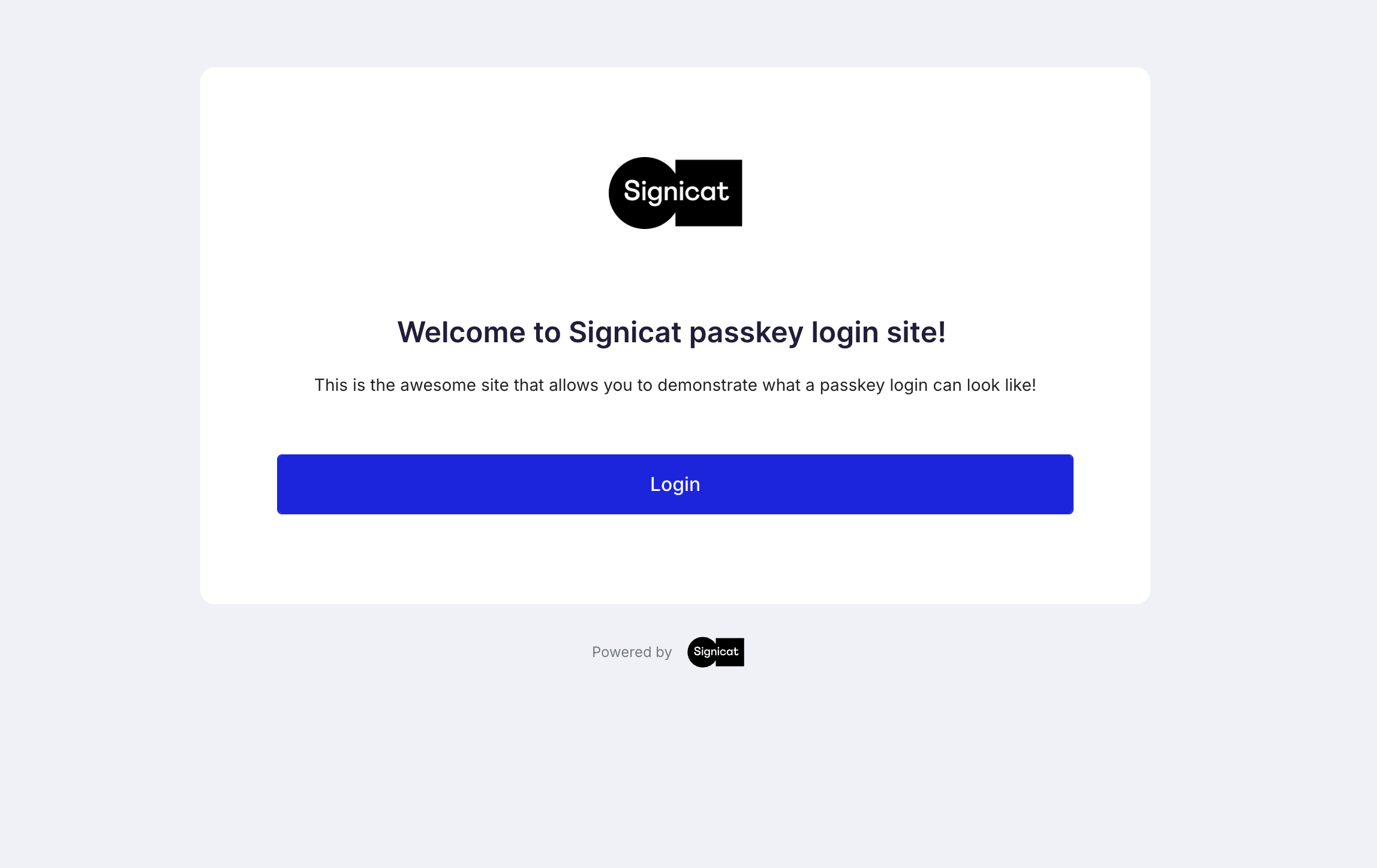
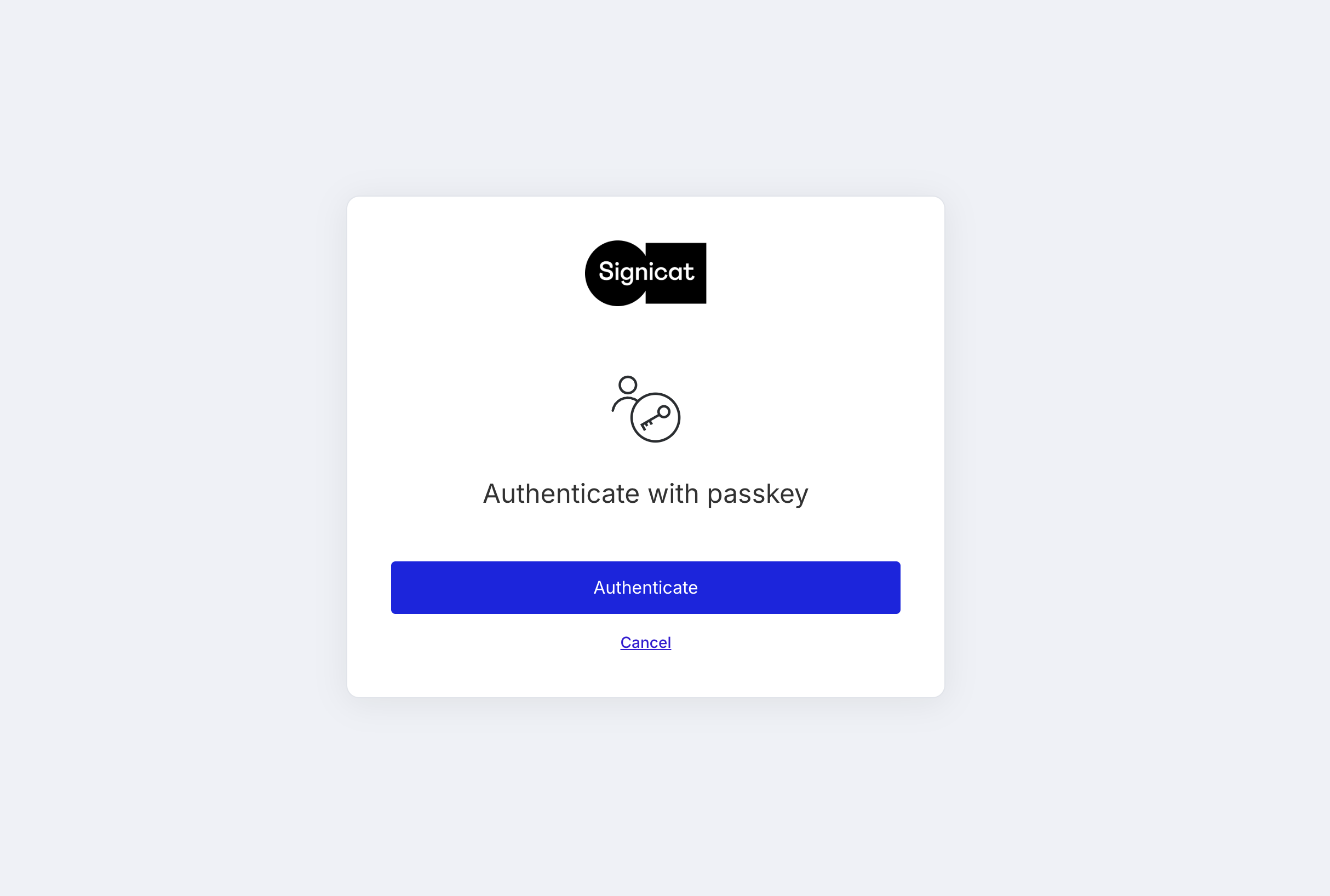
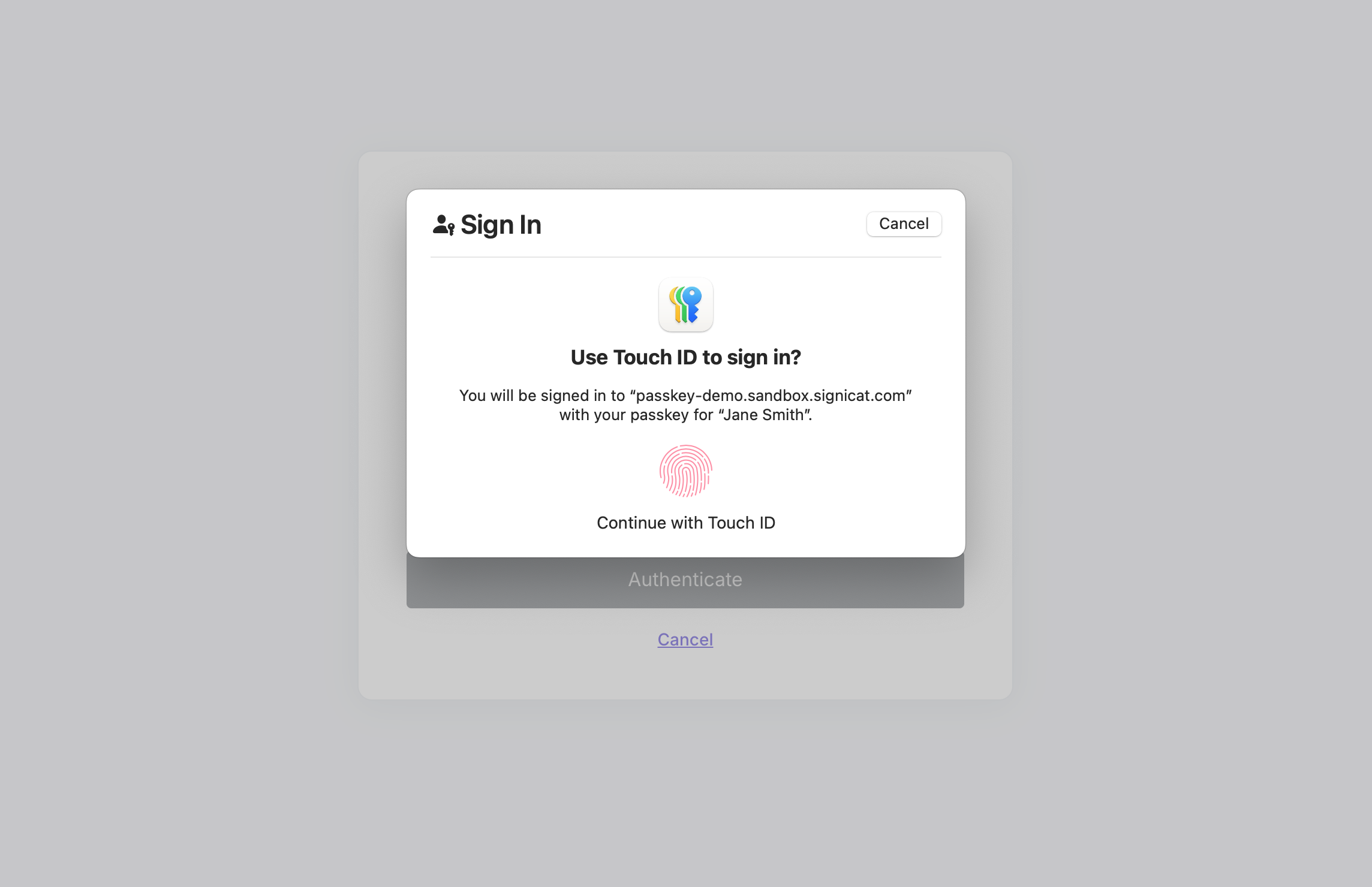
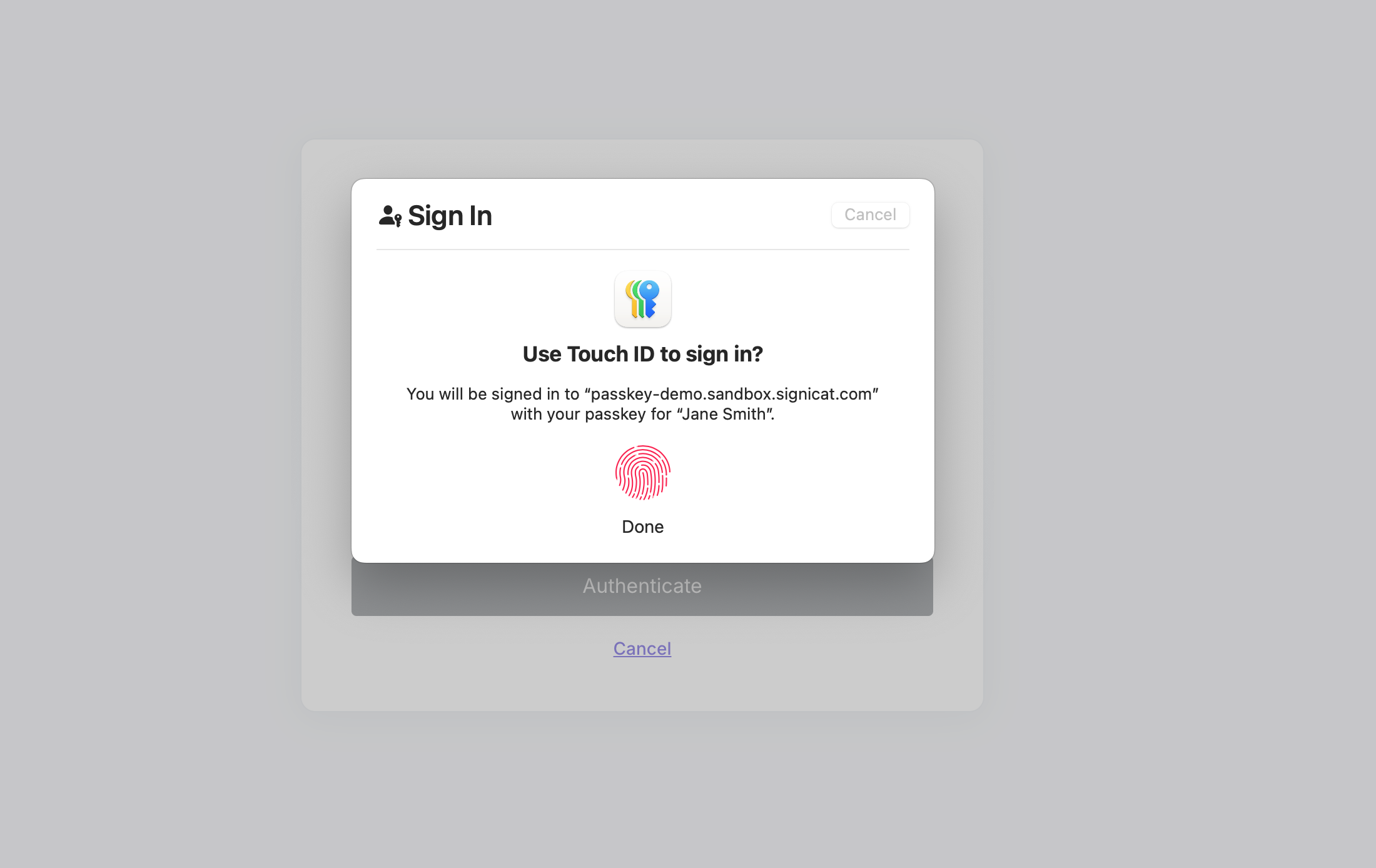
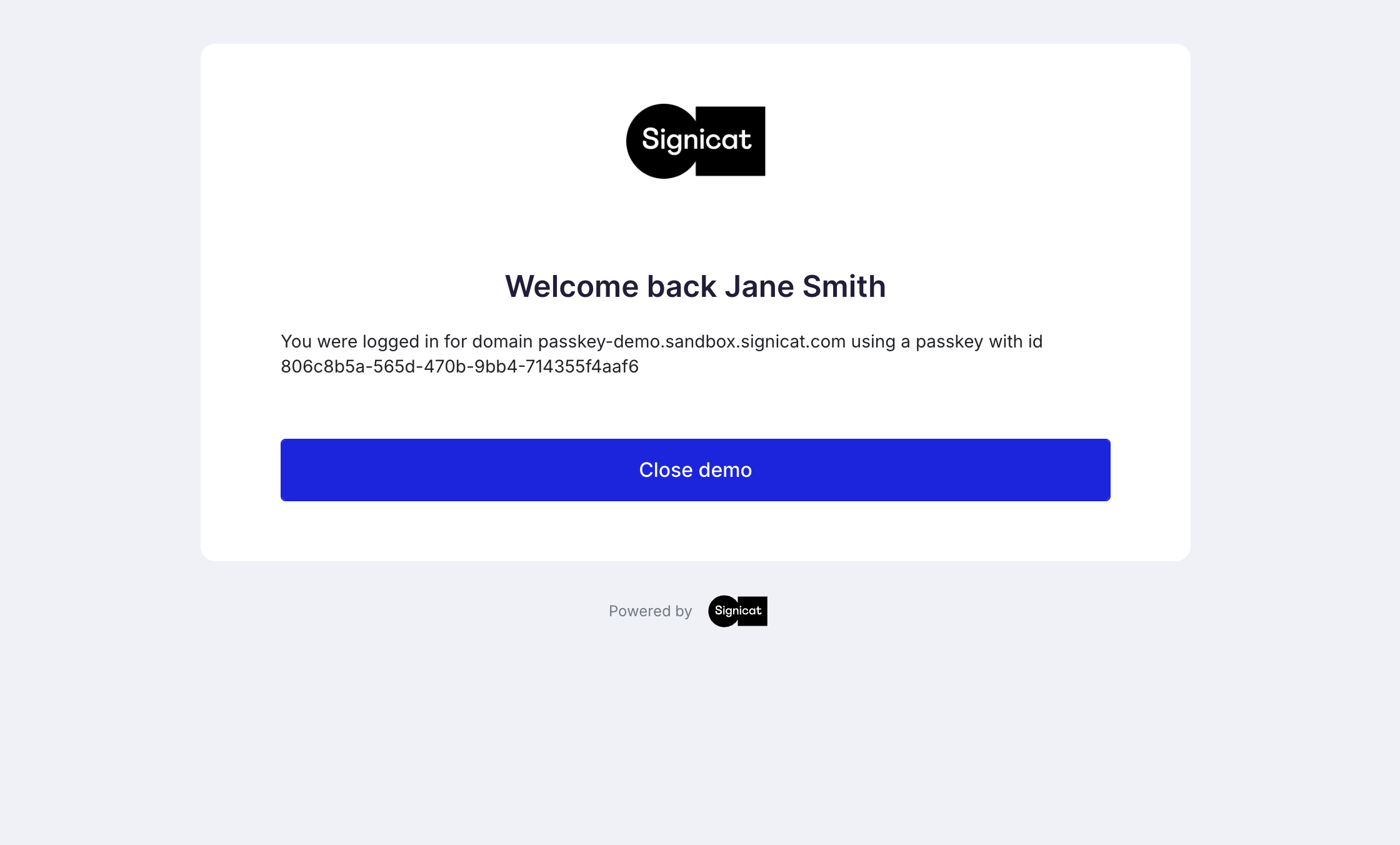
For an example of what the user interface can look like, see the image slider below:
Click to view steps
- The end-user navigates to a website in their browser, then clicks Log in with passkey.
- They are redirected to the Signicat login page. Here, they click Authenticate.
- Automatically, an overlay is shown from their key provider which asks the end-user if they want to log in.
- The end-user authenticates with biometrics on their device.
- Once authenticated successfully, the end-user is logged in.
Get started
In our quick start guide, you can learn how to use a tool of your choice to make API requests and test out ReuseID with Passkeys authentication: