How it works
Our MobileID product is comprised of two main components:
- ReuseID identity store
- Mobile authentication
These components are fulfilled by combining a ReuseID identity store for creating reusable identities with our MobileID authentication product using Encap SCA for authentications and authorisations using a mobile device.
By securely binding an end-user to a mobile device, the device can then be used to authenticate and authorise end-user operations.
Integrate with MobileID
To integrate with MobileID, there are two aspects that you need to consider:
- Backend REST API
- Mobile SDK
- Android
- iOS
You can either integrate our SDK into your own mobile app, or you can use our white-label Authenticator App which can be customised to your branding requirements.
If you choose to integrate the SDK into your own app, you have complete control over the end-user journey and experience.
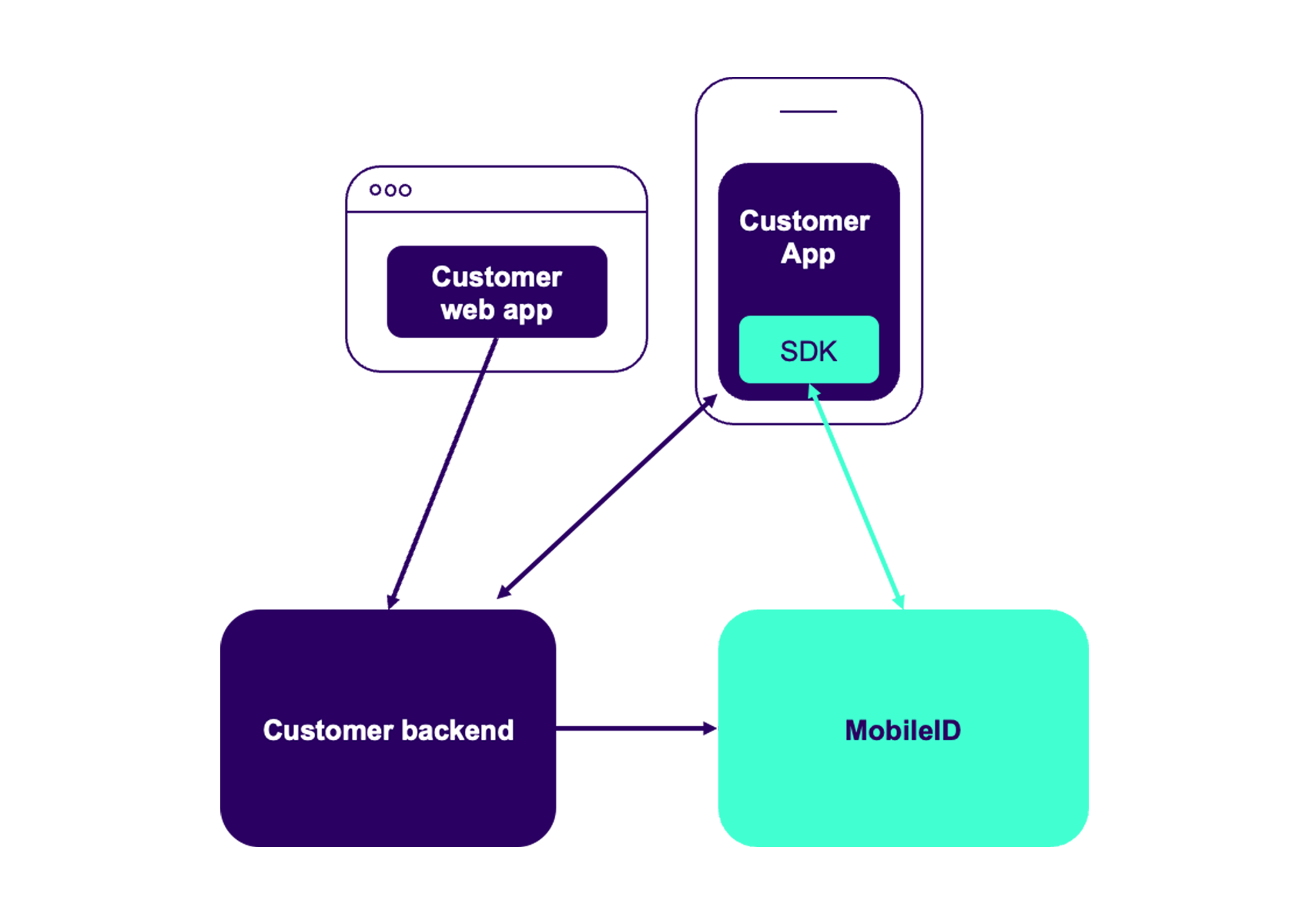
Diagram showing integration with MobileID
ReuseID identity store
Once your end-user has successfully created a ReuseID user in our identity store, they can add MobileID devices used for authentication and authorisation operations in your mobile app. A ReuseID user can have multiple MobileID devices registered.
You also have the flexibility to add any custom attributes to a ReuseID user, such as an address or phone number. Identity attributes are stored within our ReuseID identity store as key-value pairs.
The identity of a end-user is proofed outside of ReuseID. ReuseID allows you to support different proofing mechanisms depending on your target markets, whilst still using the same identity store and mobile authentication solution.
For the proofing mechanism, you can use:
- Any of our eIDs.
- Any of our electronic identity verification (eIDV) products.
- Any other proofing mechanism that you have already implemented.
User management operations
- Create new users
- Get a user and its attributes
- Update a user and its attributes
- Deactivate a user
- Lock and unlock a user
To learn more about these operations, see the User API in our ReuseID API reference documentation.
Mobile authentication
Once a MobileID device has been successfully registered for a ReuseID user, they can then be used for authentication and authorisation operations in your app.
The Encap SCA (strong customer authentication) product that MobileID uses is based on a challenge and response protocol. All communication between our MobileID backend and the SDK is secured with application layer encryption. This protects every message passed between the MobileID service and the mobile app using our SDK.
Our solution is compliant with the Payment Services Directive (PSD2) and can be used for high-value transactions.
MobileID device operations
With MobileID's device operations, you can conduct a:
Registration
This operation enables you to register a new MobileID device to an identity. An identity must have at least one registered device in order to perform any of the other device operations.
The following sequence diagram shows an example flow to register a new device for an existing ReuseID user from within your mobile app:
Sequence diagram showing MobileID registration
To learn more about this operation, see the MobileID registration API in our ReuseID API reference documentation.
Authentication and authorisation
This operation enables you to trigger an authentication or an authorisation for a ReuseID user. For all authorisations, we dynamically link the context to the transaction. This ensures compliance with the PSD2 RTS.
It can be used whenever:
- You need to verify that it is the same user accessing your services.
- You need the user to confirm a transaction.
- You need the user to perform a payment authorisation.
The following sequence diagram shows an example flow to initiate and complete an authentication or authorisation operation from within your mobile app:
Sequence diagram showing MobileID authentication
To learn more about this operation, see the MobileID authentication API in our ReuseID API reference documentation.
Consent signature
This operation is similar to the authorisation operation, however, we return a signed JWT of the transaction. This JWT can be stored and used to prove that the transaction occurred and was authorised by the user.
The following sequence diagram shows an example flow to initiate and complete a signing operation from within your mobile app:
Sequence diagram showing MobileID signature
To learn more about this operation, see the MobileID signature API in our ReuseID API reference documentation.
Device operation endpoints
Each device operation has three endpoints:
- Start an operation
- Get status of an operation
- Cancel an operation
Device operation steps
Each device operation consists of three steps:
1. Initiate the operation
To initiate an operation, a request must be made to our REST APIs. You can learn about the different MobileID operations in our ReuseID API reference documentation.
2. Carry out the operation on the device
Once an operation has been initiated, it is carried out from within your application using our SDK. Most of our SDK APIs consist of a start and a finish operation.
You can learn about our SDKs in our iOS and Android SDK documentation.
3. Finalise the operation
When the operation is completed on the device and our service has verified the operation, we will send a callback notification to your server with the result of the operation.
Device management operations
Device management operations are API calls that allow you to manage all devices in your MobileID identity store. They do not require any device interaction.
For example, you can:
- Get device information
- Deactivate a device
- Lock and unlock a device
To learn more about these operations, see the MobileID device management API in our ReuseID API reference documentation.