Stack trace
About stack trace
The Encap SDK is obfuscated. This means that exceptions generated by the SDK contain obfuscated names instead of actual name classes.
This appendix shows you how to retrace a stack trace containing Encap SDK obfuscated names.
How to retrace a stack trace
Tools
To obtain the original stack trace without any code obfuscation, you can use one or more of the following:
This tool is bundled into the command line tool package https://developer.android.com/studio/command-line/retrace.
It requires:
- A path to a mapping file.
- A path to a file that contains a stack trace or stack trace from standard input
retrace mappingFile [stackTraceFile].
This tool can be found in the Android SDK directory under tools/proguard/bin/proguardgui.sh.
Running this shell script will start the ProGuard program. The ReTrace tab allows you to input a mapping file and load a stack trace.
Example: Input a mapping file and load a stack trace in ProGuard GUI
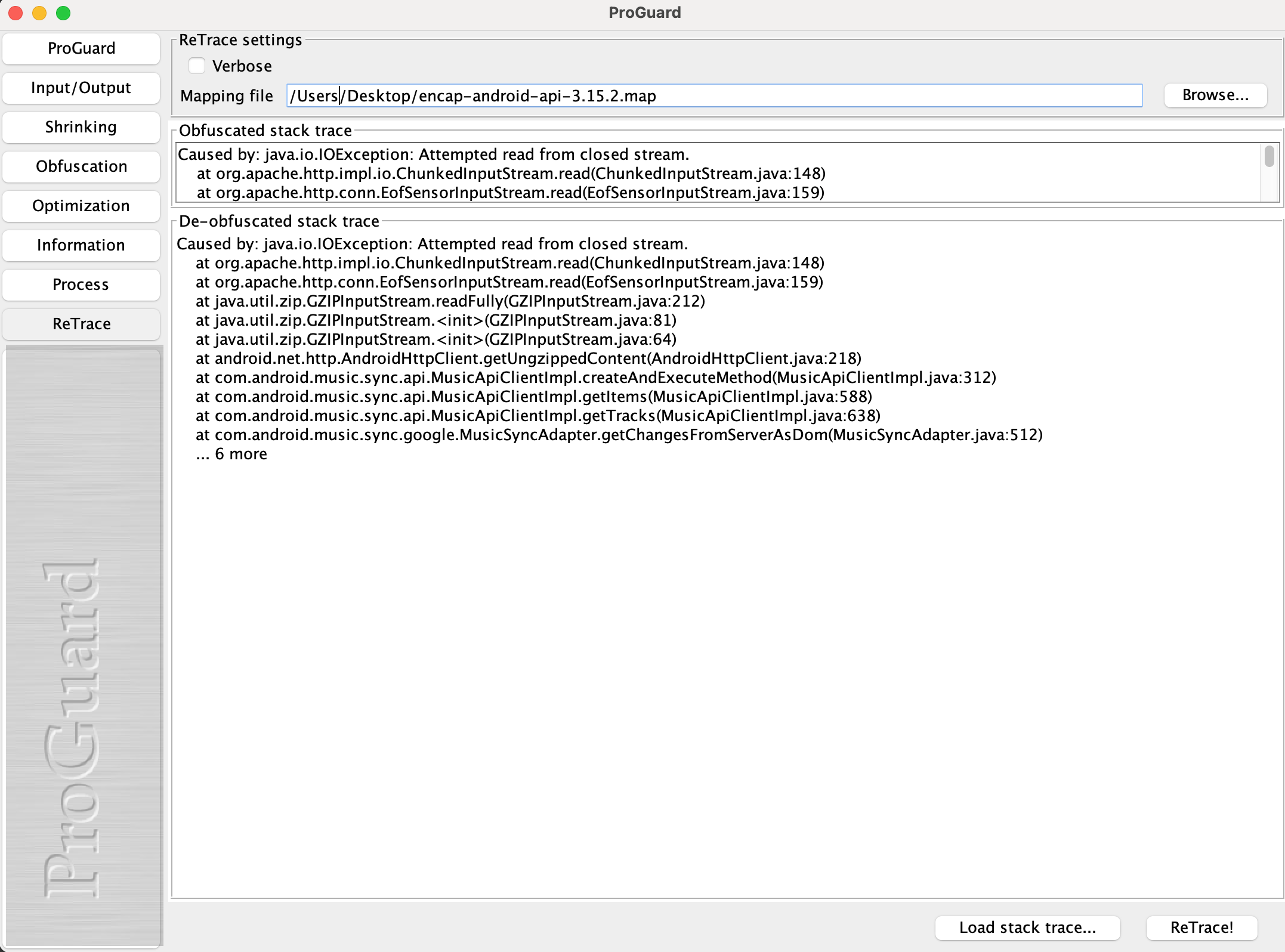
Screenshot showing ReTrace in ProGuard GUI
Mapping file
You can find the mapping file for retracing the Encap API in the Nexus repository server directory, alongside the Encap Android API library .aar file. The mapping file has a .map extension.
Each release of the Encap API has its own map file which is needed to retrace a stack trace from the Encap API.
Retracing a stack trace from an obfuscated build
When the application is obfuscated, you can retrace the stack trace from the specific build of the app by supplying the
mapping file of the specific build to the retrace command.
You can typically find the mapping file at build/outputs/mapping/release/mapping.txt.
Example: Use the retrace command for an obfuscated app
$ retrace app/build/outputs/mapping/release/mapping.txt
Waiting for stack-trace input...
com.encapsecurity.encap.android.client.api.exception.AuthenticationFailedException[message=Incorrect response to authentication challenge., isRecoverable=true, errorCode=serverErrorAuthenticationFailed, remainingAttempts=2]
at java.lang.reflect.Constructor.newInstance0(Native Method)
at java.lang.reflect.Constructor.newInstance(Constructor.java:343)
at od.o(:4)
at yq0$a.b(Unknown Source:21)
at fo0$a.e(Unknown Source:22)
at jj0.<init>(Unknown Source:3)
at jw0.l(Unknown Source:13)
at hw0.run(:1)
at java.lang.Thread.run(Thread.java:1012)
^D
com.encapsecurity.encap.android.client.api.exception.AuthenticationFailedException[message=Incorrect response to authentication challenge., isRecoverable=true, errorCode=serverErrorAuthenticationFailed, remainingAttempts=2]
at java.lang.reflect.Constructor.newInstance0(Native Method)
at java.lang.reflect.Constructor.newInstance(Constructor.java:343)
at com.encapsecurity.nz.cp(nz.java:0)
at com.encapsecurity.bph$cp.b(bph.java:21)
at com.encapsecurity.bix$cp.cp(bix.java:22)
at com.encapsecurity.aqj.<init>(aqj.java:3)
at com.encapsecurity.kc.l(kc.java:13)
at com.encapsecurity.kc.cp(kc.java:0)
at com.encapsecurity.kc.bps(kc.java:0)
at java.lang.Thread.run(Thread.java:1012)
Retracing the stack trace from an obfuscated API
When the API is obfuscated, you can retrace the stack traces containing obfuscated names in com.encapsecurity.* by supplying the mapping file of the API.
Example: Use the retrace command for an obfuscated API
$ retrace encap-android-api.map
Waiting for stack-trace input...
com.encapsecurity.encap.android.client.api.exception.AuthenticationFailedException[message=Incorrect response to authentication challenge., isRecoverable=true, errorCode=serverErrorAuthenticationFailed, remainingAttempts=2]
at java.lang.reflect.Constructor.newInstance0(Native Method)
at java.lang.reflect.Constructor.newInstance(Constructor.java:343)
at com.encapsecurity.nz.cp(nz.java:0)
at com.encapsecurity.bph$cp.b(bph.java:21)
at com.encapsecurity.bix$cp.cp(bix.java:22)
at com.encapsecurity.aqj.<init>(aqj.java:3)
at com.encapsecurity.kc.l(kc.java:13)
at com.encapsecurity.kc.cp(kc.java:0)
at com.encapsecurity.kc.bps(kc.java:0)
at java.lang.Thread.run(Thread.java:1012)
^D
com.encapsecurity.encap.android.client.api.exception.AuthenticationFailedException[message=Incorrect response to authentication challenge., isRecoverable=true, errorCode=serverErrorAuthenticationFailed, remainingAttempts=2]
at java.lang.reflect.Constructor.newInstance0(Native Method)
at java.lang.reflect.Constructor.newInstance(Constructor.java:343)
at com.encapsecurity.encap.android.client.internal.exception.ErrorCodeExceptionFactory.cp(ErrorCodeExceptionFactory.java:0)
at com.encapsecurity.encap.android.client.internal.communication.response.Response$JsonResponse.b(Response.java:21)
at com.encapsecurity.encap.android.client.internal.communication.response.CancelSessionResponse$CancelSessionJsonResponse.cp(CancelSessionResponse.java:22)
at com.encapsecurity.encap.android.client.internal.communication.response.FinishResponse.<init>(FinishResponse.java:3)
at com.encapsecurity.encap.android.client.internal.api.impl.AuthenticatorImpl.l(AuthenticatorImpl.java:13)
at com.encapsecurity.encap.android.client.internal.api.impl.AuthenticatorImpl.cp(AuthenticatorImpl.java:0)
at com.encapsecurity.encap.android.client.internal.api.impl.AuthenticatorImpl.bps(AuthenticatorImpl.java:0)
at java.lang.Thread.run(Thread.java:1012)