Hardware-protected keys
About hardware-protected keys
In addition to dynamically generated software keys, we use hardware-protected keys to strengthen proof-of-possession and maximise device security.
With hardware-protected keys, the probability that an attacker will be able to obtain the private keys that are stored in the secure hardware on a device, and then use them outside the device without breaking the device on a hardware level, is very low.
How do hardware-protected keys work?
A hardware-protected key pair is generated in hardware, typically on a trusted execution environment (TEE) or trusted platform module (TPM). The private key will never leave the hardware. As a result, all operations that require the private key are performed in the secure hardware on the device. For example, operations like encrypt, decrypt, sign and verify using the private key will be performed in the secure hardware.
Even a rooted device still protects the hardware keys from extraction, and cloning of a key can not be performed on a rooted device. It is therefore very unlikely that an attacker is able to steal a key stored in the secure hardware and use it outside of the device.
Activation
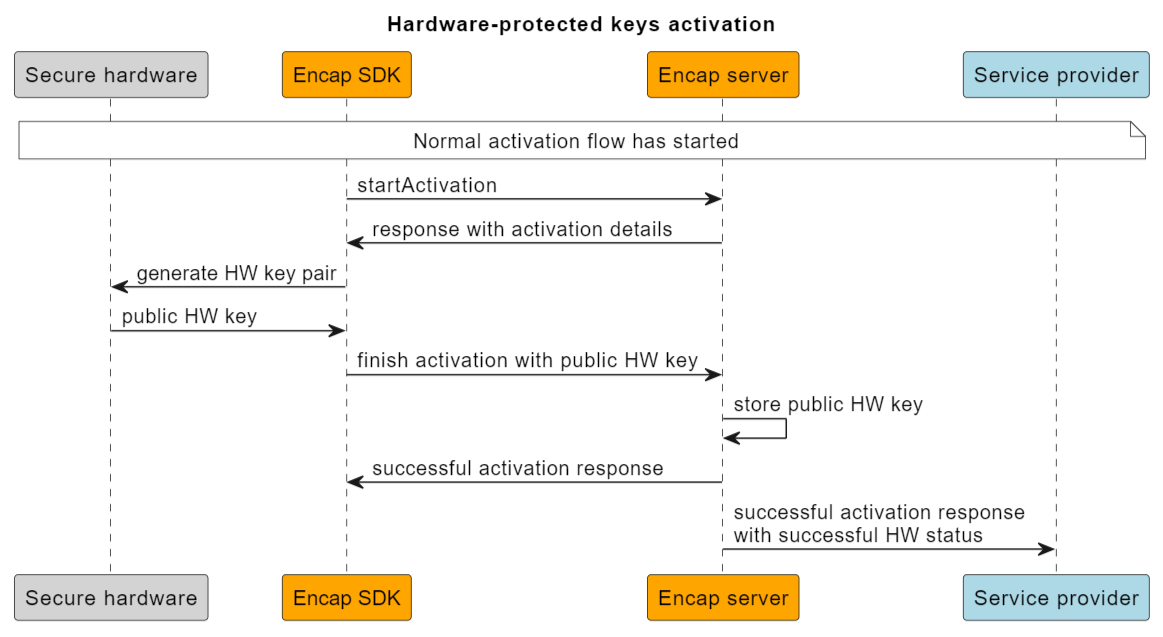
Sequence diagram showing hardware-protected keys activation
A typical flow for activation of a hardware-protected key is as follows:
- The Encap SDK generates a key pair in the secure hardware.
- The secure hardware returns the public hardware (HW) key to the Encap SDK.
- The Encap SDK returns this key to the Encap server over the secure channel in the
finish activationrequest. - The Encap server stores the public HW key on the registration, and this key will be used to verify all future authentications.
Authentication
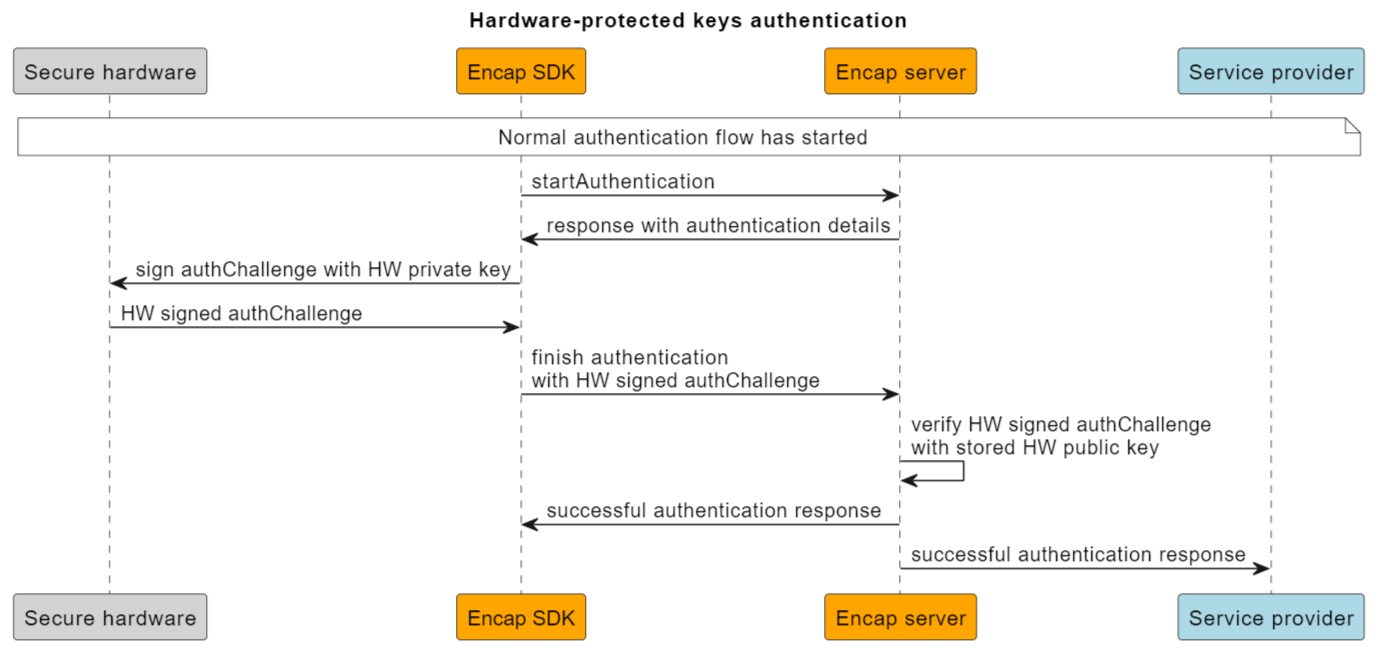
Sequence diagram showing hardware-protected keys authentication
For a device that is activated with HW keys, an additional security check will be executed for each authentication. The flow is as follows:
- The Encap SDK signs the authentication challenge received from the Encap server in the
start authenticationrequest, with the hardware-protected private key. - The signed challenge is passed back to the Encap server in the
finish authenticationrequest over the secure channel. - The signed challenge is verified on the server side with the HW public key.
Supported devices
Hardware-protected keys are supported on the following devices:
- Most devices using Android 6 devices.
- All devices using Android 7 or later.
- All devices using iOS 10 or later / devices with Secure Enclave.
Devices that do not support hardware-protected keys will only use software keys.
Requirements
- Encap client SDK version 3.8 or later.
- Encap server version 3.8 or later.
How to configure hardware-protected keys
Configure the mobile SDK
You do not need to configure the client to enable this feature.
Configure the application configuration
Learn how to configure the application configuration for app attestation.
Validation strategies
We offer two different validation strategies SUPPORTED and RISK_PARAMS.
The HW signature is validated on the Encap server for both strategies.
This is the default validation strategy. When SUPPORTED is set, the operation will fail if the hardware signature is invalid.
When RISK_PARAMS is set, the operation will not fail if the hardware signature is invalid, but it will return the hw_key_client_status and hw_key_server_result risk attributes. This enables you to evaluate the result and take action accordingly.
Setting the properties
The validation strategies are configured in the application configuration. See the tables below for details.
The result of the hardware signature validation is always returned as a part of the risk data set. This requires the application configuration to enable these parameters.
When the risk attributes are enabled, the service provider will get the result of the hardware-protected key validation in the following risk attributes:
For possible values, see the tables under Hardware protected key client statuses and Hardware protected key server result in our API reference documentation.
Rolling out hardware-protected keys
The hardware-protected keys feature was introduced in Encap 3.8. Devices that have support for HW keys and are activated with Encap SDK and server 3.8. or later will use this security feature by default.
Hardware-protected keys will be generated on all devices that are activated with Encap SDK and server 3.8. or later, given that the device has support for HW keys.
Existing and new customers
All users that activate or reactivate on Encap SDK and server 3.8 or later will automatically start using hardware-protected keys on their device.
There is no support for generating HW keys on an already activated device. Generating HW keys requires a new activation or a re-activation.