Face authentication
About face authentication
Our face authentication feature is an authentication method that uses server-side biometrics.
Server-side biometrics are authentication methods that are independent of the device. This means that they can offer cross-device compatibility and centralised management.
The face authentication method performs a two-second facial scan with 3D Liveness Check and 3D Face Matching on each authentication. This is done within a mobile app and verified on the server, preventing unauthorised access to an account.
A Liveness Check (also referred to as liveness detection) means that we will verify that it is a physical human in front of the device. We ensure that it is not a photo, deepfake video, or similar spoofing tool.
You can read more about biometric liveness detection on the liveness.com web page.
A 3D Face Matching means that we will verify that the human performing the authentication is the same as the one who activated face authentication initially. To do this:
- At the time of authentication, a 3D FaceMap is collected together with the liveness data.
- We match this 3D FaceMap to the 3D FaceMap that we collected during the activation of this authentication method.
Example use cases
Server-side biometrics have the potential to support multiple new use cases, such as:
- You want a fast and secure way to perform biometric authentication across devices, in scenarios where native biometrics are not enough.
- You want a solution if your end-users have invalidated their native biometrics.
- You want your end-users to be able to securely reset their authentication credentials.
- You want to recover your end-user's account if:
- Their device has been lost, broken or stolen.
- They have deleted your application.
- See our Account recovery feature documentation.
Coming in a future release
- You want to prevent phishing attacks when your end-users onboard.
- If the end-user is on another device.
- If multiple end-users want to use biometrics on the same device.
What is the difference between Face ID and face authentication?
Native biometrics
Native biometrics are authentication methods provided by the device's operating system, executed and validated directly on the device for quick and secure authentication using the device's hardware and software.
Some examples of native biometrics are Apple Face ID, Apple Touch ID and Android BiometricPrompt.
Native biometrics are fast, secure, and offer a great user experience. We recommend using native biometrics whenever possible.
Server-side biometrics
Server-side biometrics are authentication methods that are independent of the device. These methods offer cross-device compatibility and centralised management, which means that they can be leveraged in some use cases where native biometrics will not work.
An example of server-side biometrics is our face authentication feature.
How does face authentication work?
As with all other authentication methods, face authentication needs to be activated before end-users can start using it.
Once you have activated face authentication for your end-users, you can use it to:
- Authenticate (see section on this page)
- Reset authentication credentials
- Perform account recoveries (see section on this page)
- Prevent fraud during onboarding (possible in a future release)
Activation and authentication operations using face authentication are subject to quota limits.
For default quotas and more information, see the Quotas section.
Basic flow for a face authentication
- A FaceMap is captured on the end-user's device.
- The captured FaceMap is securely transmitted to our server.
- The server processes and validates the FaceMap, performing the necessary authentication checks.
How to activate a device for face authentication
To activate face authentication, you first need to register a device for your end-user. Once the user has an active device, you can then add face authentication using our addOrUpdate method in the SDK.
You can learn how to do this in the Add or update sections of our SDK documentation:
What does an activation look like?
The following diagram illustrates what it could look like to activate face authentication, from the perspective of your end-users.
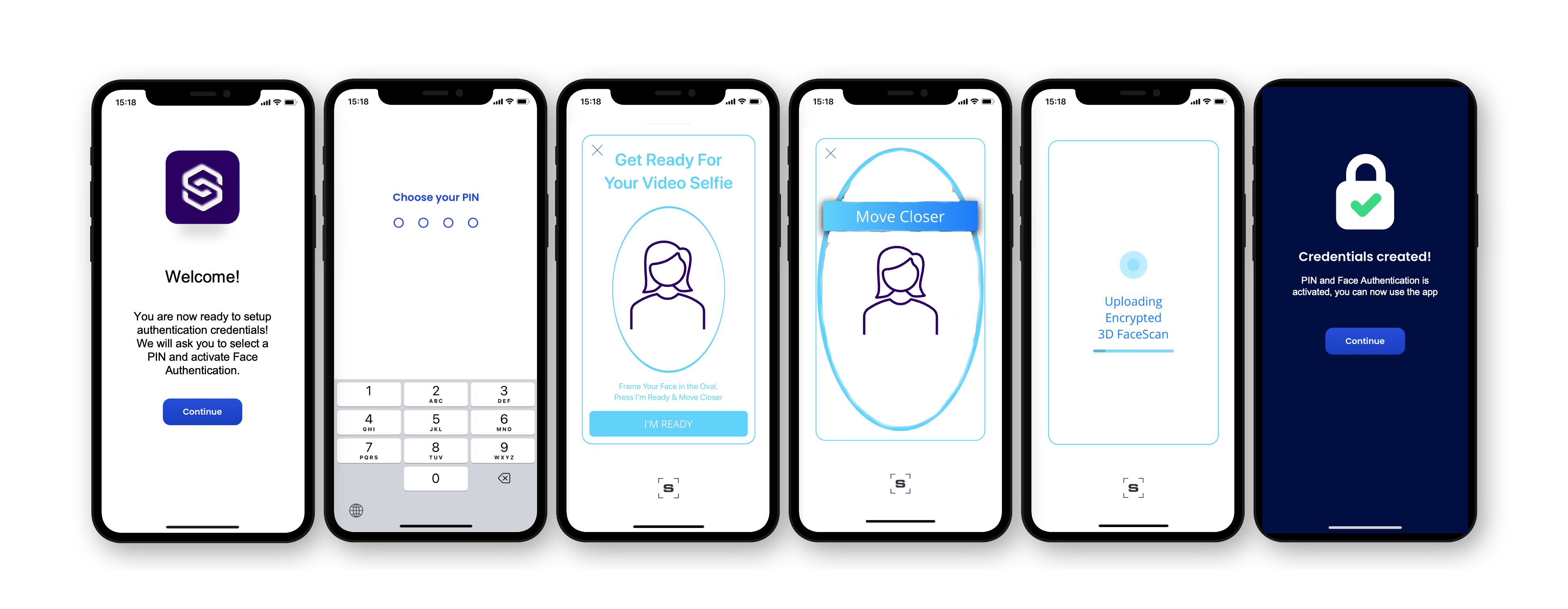
Diagram showing end-user flow for activating face authentication
Diagram for activation
The following sequence diagram illustrates an activation of face authentication.
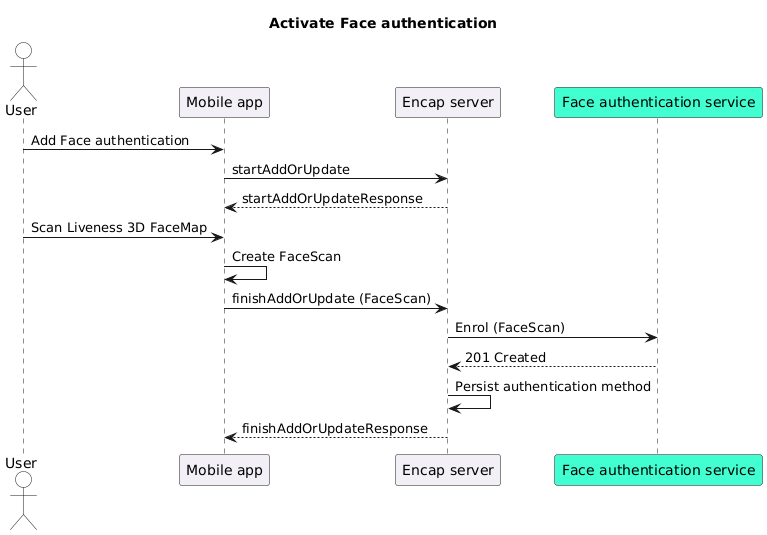
Sequence diagram showing activation of face authentication
How to authenticate with face authentication
You can initiate a face authentication by setting DEVICE_SERVER_SIDE_FACE as the authMethod when you start the authentication operation.
See Authentication methods in the Encap API reference documentation for details.
What does an authentication look like?
The following diagram illustrates what it could look like to authenticate with face authentication, from the perspective of your end-users.
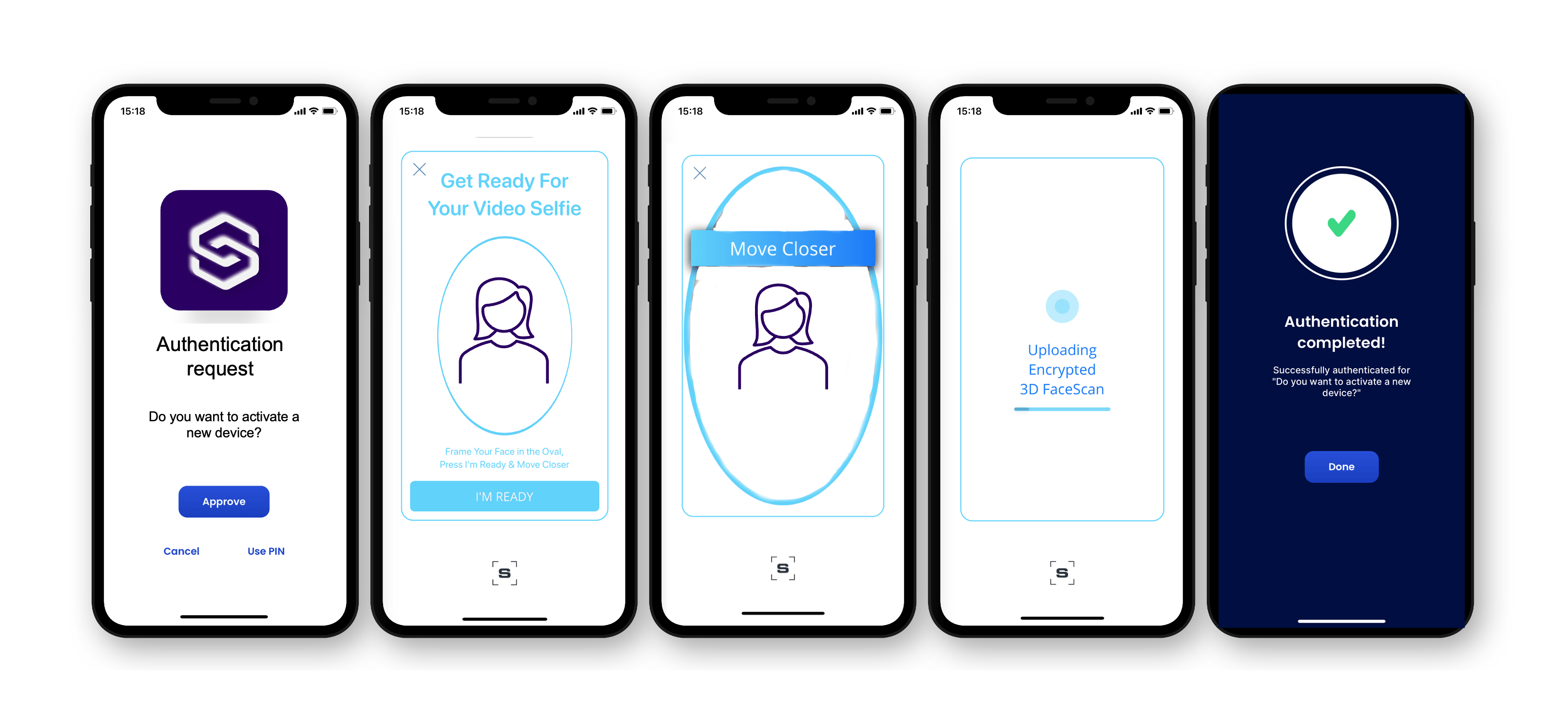
Diagram showing end-user flow for authentication with face authentication
Diagram for authentication
The following sequence diagram illustrates an authentication with face authentication.

Sequence diagram showing authentication with face authentication
How to recover with face authentication
Our account recovery feature supports server-side face authentication as an authentication method. We recommend this for recovery, as:
- It is more user-friendly, with no recovery code to remember.
- It enhances security by not having a recovery code which could be shared.
To learn about this feature and how to implement it, see our Account recovery feature documentation.
API integration
The following service provider REST APIs have been extended with the DEVICE_SERVER_SIDE_FACE authentication method.
Activation
The activated_authentication_methods field can contain DEVICE_SERVER_SIDE_FACE for enrolment operations.
For further details, see The enrollment object in our Encap API reference documentation.
Authentication
The authentication_method parameter can contain DEVICE_SERVER_SIDE_FACE for authentication operations.
For further details, see Authentication in our Encap API reference documentation.
Device object
The activated_authentication_methods field in the device object can now contain DEVICE_SERVER_SIDE_FACE.
For further details, see The device object in our Encap API reference documentation.
How to configure face authentication
To use our face authentication feature, you need to:
- Contact Signicat to get access to this feature.
- Configure the mobile SDK.
- Configure the application configuration.
Configure the mobile SDK
Learn how to configure the mobile SDK for face authentication.
Configure the application configuration
To enable the server-side authentication method, you need to update your application configuration with the following parameters:
Quotas
All performed activation and authentication operations which use face authentication are subject to the default quota limits.
If your app exceeds the default quotas outlined in the tables below, then your requests may fail. To update the quota limits, you can contact us by creating a support ticket in the Signicat Dashboard.
Production environment
Default quotas in the production environment:
| Quota name | Default limit |
|---|---|
Face authentications per account per day | 1000 |
Face authentications per account per minute | 10 |
Face registrations per account per day | 1000 |
Face registrations per account per minute | 10 |
Sandbox environment
Default quotas in the sandbox environment:
| Quota name | Default limit |
|---|---|
Face authentications per account per day | 100 |
Face authentications per account per minute | 10 |
Face registrations per account per day | 100 |
Face registrations per account per minute | 10 |