Single Sign-On
Single Sign-On (SSO) allows you to keep users logged in across multiple services over time. When you enable SSO, your users only need to log in the first time they access your app without having to authenticate again when they come back later.
Currently, we only support SSO at the eID and Wallet Hub level for SAML 2.0. Therefore, the information on this guide only applies to SAML 2.0. We also support SSO at the OIDC level. Learn more about SSO for OIDC in the OIDC implementation guide.
How SSO works
The eID and Wallet Hub SSO stores a token (session cookie) in the browser of the user to identify them when they return to authenticate with your application. The token does not contain any personal identifiable information. Based on the token and the parameters in the authentication request (for example, LoA and attributes), the eID and Wallet Hub checks whether the SSO is still applicable and handles the authentication appropriately.
When you activate SSO in the eID and Wallet Hub, Signicat keeps the login response for a user session after a successful login transaction. The next time (within the same session) a new login transaction starts, the end user will not have to log in again. Instead, the same response that Signicat stored in the first login transaction will be automatically returned to your application. The response will contain the same subject identifier and any other attribute you requested previously.
The SSO process happens within the context of a user session. If the user closes the browser, SSO will terminate and the user must re-authenticate. Technically, this means that the SSO is non-persistent.
Levels of SSO
Note that SSO may occur at different levels. We distinguish between the following levels:
- eID and Wallet Hub (described on this page)
- OIDC server (see the OIDC documentation)
- IdP or eID (depends on the identity provider)
When integrating with an eID using the Signicat eID and Wallet Hub, it is important to consider the interactions that might occur between different SSO levels.
Technical considerations
Note that SSO does not work when:
- The IP of the end-user changes from one authentication to the next.
- The level of assurance (LoA) requested in a subsequent request is higher than the LoA used in the initial login.
- Your account configuration changes between sessions so that the authentication provider is no longer active in your account.
- You scope an eID (see IdP scoping) differently than in the initial request.
- You send an OIDC authentication request with
prompt=login. - You send a SAML authentication request with
forceAuthn=true. - You connect using the Signicat Authentication REST API, which does not support SSO.
In any of the above scenarios, the end-user must re-authenticate.
Enabling SSO
You can enable SSO at the eID and Wallet Hub level in the Signicat Dashboard. To do this:
- Log in to the Dashboard.
- Navigate to Products > eID and Wallet Hub > Settings.
- Select Enabled in the SSO settings dropdown.
SSO session management settings
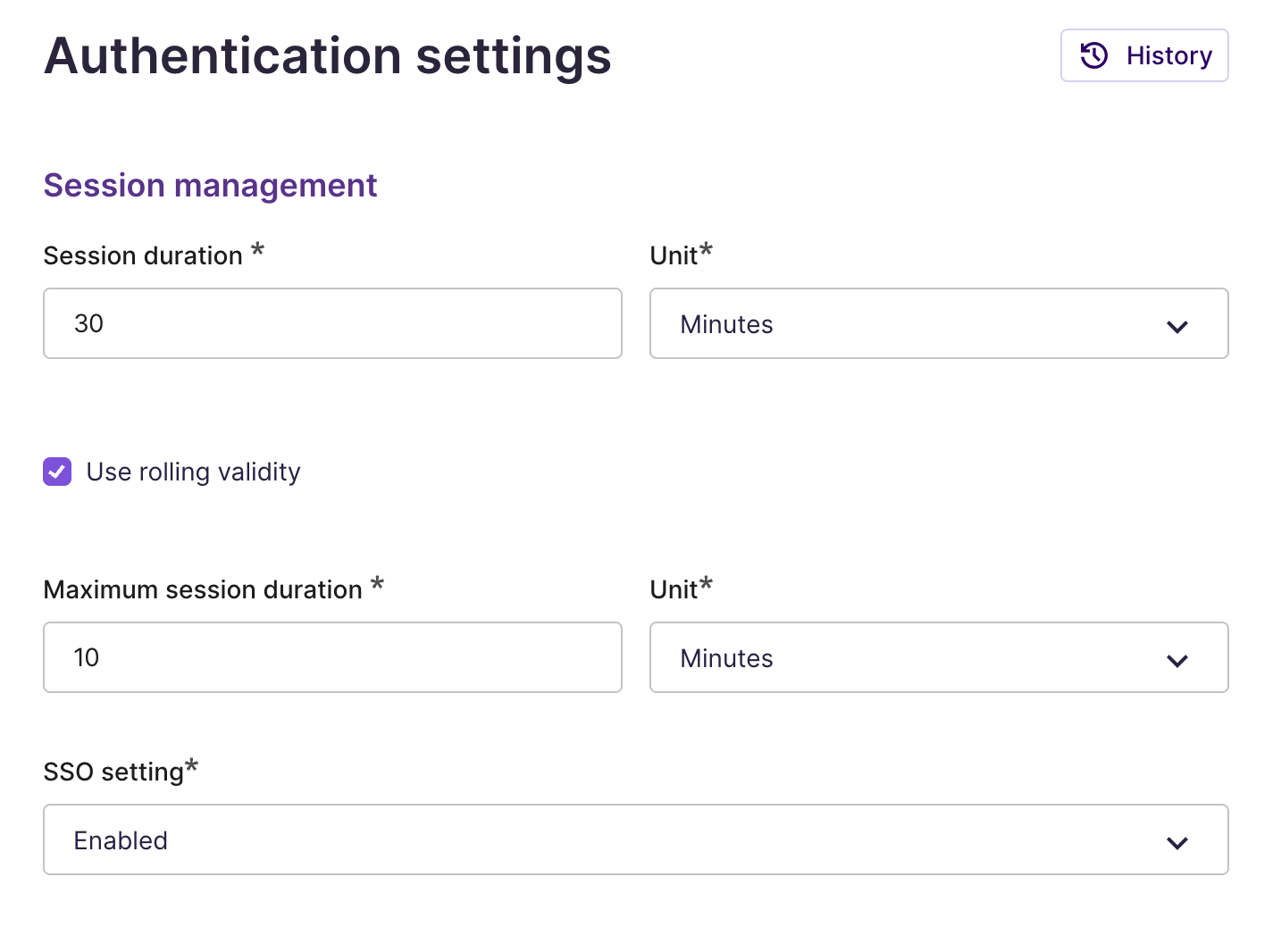
- Configure the SSO-related settings:
- Scroll at the bottom of the page and select Save to persist the changes.
After you enable SSO, these settings apply to all future authentication transactions started using this account.
When you enable SSO in the Signicat Dashboard, SSO is configured at the account level.
All authentications transactions with SAML 2.0 for this account will enforce SSO, by default.
Skipping SSO
You can bypass the SSO configuration in the Dashboard by providing specific parameters in an authentication request. How to do this varies per authentication protocol.
When bypassing SSO in your authentication request, SSO is skipped across all levels. Therefore, end-users must always re-authenticate, regardless of any other SSO level configuration.
- OpenID Connect
- SAML 2.0
- Authentication REST API
When sending an authentication request with OIDC, the prompt attribute allows you to ignore any existing session and prompt the user to re-authenticate. To do this, set the prompt=login parameter in your authentication request, as shown below:
https://example.sandbox.signicat.com/auth/open/connect/authorize?
client_id=sandbox-vivid-blade-759
&response_type=code
&redirect_uri=https://oauth.tools/callback/code
&state=1734687023840-WGZ
&scope=openid%20profile%20nin
&code_challenge=7aEnwazbpKXHjOYbISsHWbtAWn33fE9cgDpS0y4-0UM
&code_challenge_method=S256
&prompt=login
The above request bypasses SSO and prompts the user to re-authenticate.
Note that SSO is still enabled for future requests without prompt=login. Skipping SSO is transient and different from forcing logout.